So to understand how you can protect yourself against the malicious attackers looking to install their malware on your PC, you have to know what programs attackers are exploiting. Keeping your software up to date with security patches is vital. The top applications that attackers are having success with when it comes to running exploits on your PC include the following:
- Java Runtime Engine (JRE)
- Adobe Reader/Acrobat
- Adobe Flash Player
It is also important to know that these aren't the only things you need to update. Microsoft updates are important. If you don't already have them set to automatically download and install, you should do this. Updating applications like iTunes, QuickTime, Firefox, just to name a few.
It is also important to have some sort of anti-virus installed on your PC and it should be set up to scan on a regular schedule and keep the signatures up to date. I also recommend that you install a great malware removal tool called Malwarebytes Anti-malware. Download and install the free version. You can find it
here.
Lastly, your actions can go a long ways in keeping malware off your PC. Knowing if you should click or not IS a really big deal. If something doesn't look right it probably isn't.
These are just a few steps you can take to keep malicious software from being installed on your PC. Protect your family and your financial health from the cyber attackers. Stay safe out there.
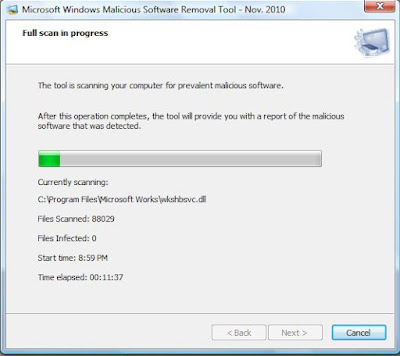
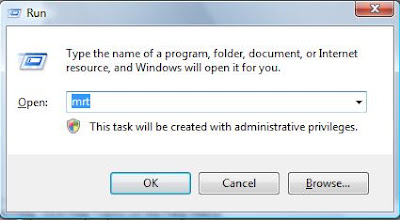 You just type 'mrt' in the input box and hit the OK button. This will bring up the dialog box for the MRT.
You just type 'mrt' in the input box and hit the OK button. This will bring up the dialog box for the MRT.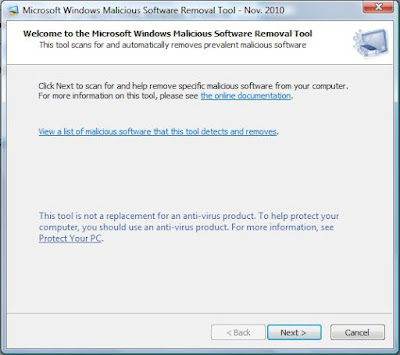 Now you just click on the Next> button and you will be presented with the following dialog box.
Now you just click on the Next> button and you will be presented with the following dialog box.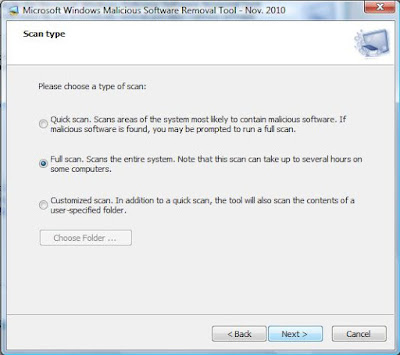 You then select the Full Scan radio button and click on the Next> button to start the scan off. It may take some time to actually complete, but this will give you another layer of security for your home PC.
You then select the Full Scan radio button and click on the Next> button to start the scan off. It may take some time to actually complete, but this will give you another layer of security for your home PC.